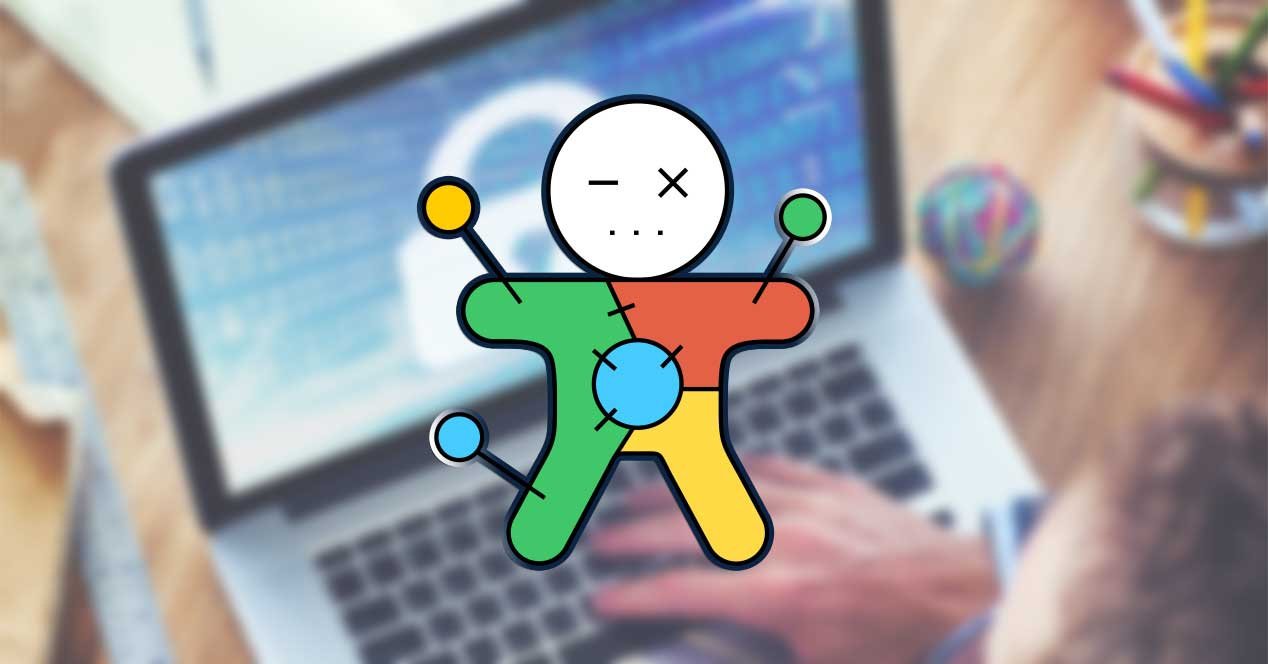
Try2Cry “Stupid” Ransomware
Ransomware attacks are unprecedentedly rising during COVID times. The increase in such attacks is rampant and involves advanced and highly notorious techniques. But all attacks do not fall in the same severity level. Recently, a… Try2Cry “Stupid” Ransomware