Hackers are using the global COVID-19 pandemic to propagate the payload around several enterprises. Hackers are using NSIS as an installer to target industrial enterprises with evolving payloads, including LokiBot, FormBook, BetaBot, Agent Tesla, and Netwire.
A new cybercrime group RATicate has been pulled out by the researchers which has alleged to summon waves of malspam attacks. Evidently, this attack targets industrial companies with various information. They are stealing payloads from LokiBot to Agent Tesla. Besides, these two are the RAT(Remote Access Trojan) malware that comes with a keylogger to gather users information.
Access to your user credentials is what makes it more dangerous!
In this article, we shall evaluate the consequences as well as some deep insights of this vulnerability.
What is NSIS Installer?
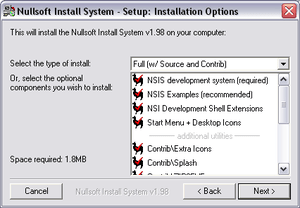
NSIS (Nullsoft Scriptable Install System) is a script-driven installer managing tool. It comes with Microsoft Windows and is supported by Nullsoft, the creators of Winamp. Also, It attains under a combination of free software licenses, primarily the Zlib license. The attack comprises of an attached document which varies between campaigns and included.ZIP, .IMG, .UDF, .RTF and.XLS files. NSIS acts as a mediator between your operating system and package installer, that’s what makes it boon for hackers. It has long been abused by bad actors to disguise and deploy malware.
Insights of the attack!
NSIS installers use a plugin architecture, which enables them to communicate with various software components including Windows OS components, which are deployed as Windows DLL files. These plugins later facilitate with various capabilities, including killing processes, executing command line-based programs, dynamically decompressing files or loading a DLL and calling to its exports. Those all components mentioned above indicate that the NSIS installers use a System.dll plugin, which then allows attackers to load a DLL and call its exported functions. Such actions may lead to devastating results.
Investigators found that the installers used in campaigns have got their consideration because it dropped the same set of junk files. These files were never used by the installed malware, researchers assume it to be an anti-analysis method.
“We’ve seen the tactic of packing NSIS installers with garbage files to conceal malware in the past; the junk files are intended to confuse analysts and create ‘noise’ during sandbox analysis,” said researchers.
Once the installer executes the executable file, then the malicious DLL acts as the program loader. Also, it begins to decrypt the malicious payload, and then finally inject the malicious payloads into memory while the NSIS layer drops the junk files.
Associated Payloads:
Security personnel at Sophos lab has examined the payload, said “During the analysis of the samples we collected conducted both manually and with the aid of sandboxing tools we found several different families of RATs and info stealers,”
Lokibot, a payload that consists of an info stealer that chokes down several user credentials from the internal system, including FTP credentials, stored email passwords, passwords stored in the browser, and password hashes. Apart, BetaBot, which has been described as rootkit-based financial malware and Formbook, a browser form-stealer and keylogger,are also the part of payloads, being used.
Agent Tesla, a spyware havings capability to extract use credentials, copy clipboard data, perform screen captures, form-grabbing and keylogging functionality,
“It could simply be that they are dropping malware on targeted companies in order to provide paid access to others, or are using info stealer and RAT malware as part of a larger malware distribution effort,” said researchers. “We continue to analyze the new attacks and hope to get a deeper insight into their motivations.”
Observing the payloads analogy, researchers said they’re unsure of whether the group is focused on corporate espionage or is simply acting as a malware-as-a-service provider for other threat actors.
How to mitigate the attack?
To counter such hazardous payloads, you must be loaded with defence weapons. Below are some tips to neutralize the attack:
-
Make sure you update your operating system to the latest version available in the market. Eg, WINDOWS 10, and other LINUX distros.
-
Install updates to your computer security system and regularly scan your files.
-
Wisely choose antivirus software, they will be the backbone of your support system.
-
Use digital signatures. They identify download sources. That way, you can be sure the files you’re downloading and running are not risky.
-
Do not ever use any patched/modified software, they may lure you with there free price tag.