WHAT IS NextCry?
NextCry gets its name from the expansion the ransomware uses to attach the filenames of scrambled documents. The malware focuses on the customers utilizing the Next cloud file sync feature and share service. As ransomware creators are rapidly improving and improvising, another malware has recently risen in the digital world scene. The ransomware, named NextCry, has been seen as dynamic as it stays undetected by antivirus engines on public checking platforms.
HOW WAS IT DISCOVERED?
An insight concerning ransomware was uncovered after a Nextcloud client who passes by the online name of ‘xact64’ took to the Bleeping Computer gathering to talk about an approach to decode encoded records. The client noted regardless of whether his framework was updated or not, the synchronization procedure had begun to refresh and update documents on the PC with the encoded form on the server.
Afterward, the client found that a portion of the records was renamed to NextCry, also called Next-Cry. “I understood quickly that my server got hacked and those records got encoded. The principal thing I did was destroy the server to restrain the harm that was being done, just half of my documents got encoded.” clarified xact64, Bleeping Computer announced.
WHAT’S GOING ON?
Bleeping Computer found that NextCry is a Python Script accumulated in a Linux ELF paired utilizing pyInstaller. The ransomware utilizes the Base64 calculation to encode the filenames. The fascinating part of the ransomware is that it utilizes the AES-256 calculation to encode the records and that the key is scrambled with an RSA-20148 open key installed in the code of the ransomware.
At the point when executed, the ransomware first searches the target individual’s Nextcloud record share and matches up the information registry by perusing the administration’s config.php document. Afterward, it erases the document that could be utilized to reestablish documents and afterward scrambles every one of the records in the information registry.
WHAT AMOUNT OF PAYMENT DOES IT DEMAND?
The ransomware requests a payment of BTC 0.025 (generally $210) to decode the documents encoded. The payment request is dropped as a note which says,
“YOU HAVE BEEN HACKED YOUR FILES HAVE BEEN ENCRYPTED USING A STRONG AES-256 ALGORITHM – SEND 0.025 BTC TO THE FOLLOWING wallet address AND AFTER PAY CONTACT their email TO RECOVER THE KEY NECESSARY TO DECRYPT YOUR FILES”
In spite of the fact that the engendering strategy for the malware is obscure, another client who goes online with the handle ‘Palexpo’ clarifies that the aggressors abused a few vulnerabilities in the Nextcloud server to spread NextCry. Of late, on October 24, Nextcloud had discharged an urgent caution for the CVE-2019-11043 RCE in NGINX. It is assumed that this vulnerable feature was accessible to general society thus leading to the mishap.
Nextcloud clients have been prescribed to update their PHP bundles and NGINX setup documents to the most recent rendition.
PREVENTIVE MEASURES
In this exact moment, somebody is clicking a link in a spam email or actuating macros in a vindictive record without having legitimate security programming set up. In almost no time, all of their information will be encoded and they’ll have only a couple of days to accumulate hundreds of dollars to get their information back. Except if they have reinforcement or backup, which the vast majority doesn’t.
Ransomware makers and other digital crooks engaged with the malware economy are callous. They’ve mechanized their assaults to the point of focusing on anybody and everyone. Ransomware is a complex bit of malware that hinders the target individual’s entrance to his/her records, and the best way to recover access to the documents is to pay a ransom. It highlights unbreakable encryption, which implies that you can’t decode the records without taking help from someone else. It can encode a wide range of records, from archives to pictures, recordings, sound documents and different things you may have on your PC.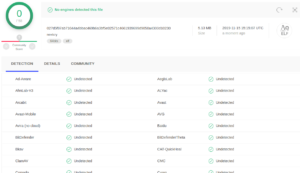
It scrambles the record names so that one can’t find which exact document was influenced. This is one of the most common social designing stunts used to confound and force unfortunate casualties into paying the payment. Followed by a picture or a message displayed on the screen informing the victim about the attack. It demands payments in Bitcoins on the grounds that this digital money can’t be followed by digital security analysts or law authorizations organizations.
WHY IS IT DIFFICULT TO TRACE THEM?
• Firstly, it deploys encrypted payloads thus making it difficult for the antivirus to identify or discover the malware, in turn allowing it to spread over multiple files.
• Secondly, using polymorphic behavior which gives it the ability to mutate enough to create a new variant, but not so much as to alter the malware’s function.
• Thirdly, malware usually focuses on the ability to remain dormant – the ransomware can remain inactive in the system until the computer is at its most vulnerable point and then strike fast and effectively.
SOME OF THE STEPS THAT CAN BE TAKEN TO AVOID FALLING VICTIM TO RANSOMWARE ATTACKS ARE AS FOLLOWS;
• Don’t store important information just on the PC.
• Have 2 reinforcements of important documents: on an outside hard drive and in the cloud – Dropbox/Google Drive/and so forth.
• The Dropbox/Google Drive/OneDrive PC shouldn’t be turned on default. Personally synchronize your information once a day.
• Avoid using the following applications; Adobe Flash, Adobe Reader, Java, and Silverlight. On the occasion that one needs to urgently use them, set the program to inquire as to whether these applications are safe to use or not.
• Expelled obsolete modules and additional items from the PC. Keep only the ones are frequently used.
• Use an advertisement blocker to evade the risk of conceivably malignant promotions.
• Avoid opening spam messages or messages from obscure senders.
• Don’t download connections from spam messages or suspicious links.
• Use a dependable, paid antivirus item that incorporates a programmed update module and a continuous scanner.
One would surely not fall victim to such malware attacks if they keep these precautionary measures in mind.

