We all hear that the worst thing that can happen to you in the cyber world is that your entire data is stolen by criminals. Guess what? That’s not the worst thing. The worst thing is when you pay the attackers to give you your data back but instead, you receive your data in an encrypted format. And the attackers ask for extra money for decrypting your data. Now that’s double trouble! And this is what we call Double extortion ransomware attacks. This strategy was known for a long time but its use has increased in 2020.
Case in point
In Double extortion attacks, the attacker tries to incite fear among the victims by creating more and more pressure. This pressure can be financial or mental. For instance, in 2019 hackers were able to get hold of the entire database of US-based suppliers of security and janitorial. The attackers threatened to leak the information out to the public if the demand of $2.3 million was not met. When the victim acted too stiff and denied cooperating, the attackers released around 10% of the data on a public forum. Later they increased the ransom amount by a whopping 50% and the victim had no other choice to pay the increased amount.
The Upsurge
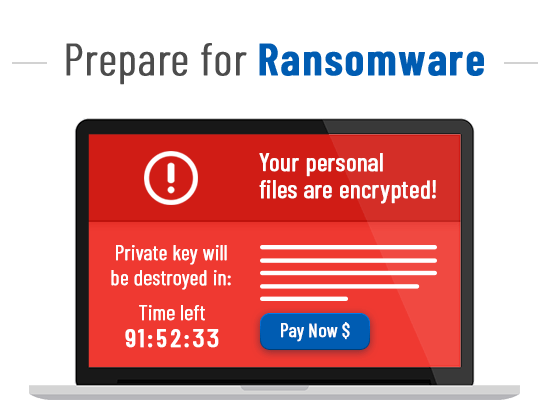
The medical industry is often seen as the biggest victim of this attack. Lack of security on digital records and barely a handful of experts handling all the data makes this industry a tempting target. As we all know, the coronavirus is putting all the hospitals under a serious test. The staff is more committed to saving lives than to follow the protocols while maintaining records. Recently, an app was circulating over the internet which claimed to be a coronavirus tracker. This app claims to track all the number of corona affected patients but what it does is fill your device with bloatware. It requests access to lock screen and other accessibility settings, which by the way are not at all required for a genuine tracking app. Then this app displays a warning message on the lock screen that your system is under danger and locked. It only allows you to unlock your device only once you agree to pay $100 in bitcoins. This app is not available on the app store but can be downloaded via websites easily accessible to the public.
Constant criticism
Attacks on medical fraternity are shameful. Targetting them is not hurting the particular organization, but also putting hundreds of lives at risk. They have received hefty criticisms from various groups around the world. A few hacker groups have also pledged not to attack these organizations in these troubled times. But it will be naïve to trust someone who is known for not staying true to his words. Hospitals should not let their guard down.

But why double ransomware?
Try to look at it from the attackers’ point of view. If you have access to precious data of an organization and they hastily agreed to pay you, then it raises some suspicion. Maybe the data that you possess is of way more important than you thought. Or maybe the organization doesn’t have a proper negotiation strategy and would have paid even more if you had asked. Or maybe this is the first time they are under any such attack and fear is getting the best out of them. So you do the obvious, you ask for more by putting some extra pressure on them.
How to tackle?
The first step is to prevent anything of this sort to occur. But if its too late and attackers have already played their move then you need to act smart. As we saw, if you are cooperating too easily and agreeing to quickly then you are pushing yourself into a bigger trap. You need to negotiate. You need to stop acting gullible. No matter how precious the data is, you can’t let them dominate. “Never split the difference” by Chris Voss is an excellent book that teaches several negotiating techniques. Mr. Voss was an FBI negotiator for more than a decade and he excelled in his profession. He shares his experience about how to interact with the attackers to get the most out of the situation. The book covers some concepts which appear to be so simple that people don ‘t think they are powerful. But when the same concept is put in a hostage narrative, it becomes riveting & memorable.



