Google developed Captcha to stop bots from accessing websites and they used it extensively. They promoted it so much so that mere listening to the word “Captcha” makes us feel that the website is secure. Recently some creative hackers were able to identify this feeling of ours and managed to fool us in a never seen before way.
Understanding Captcha
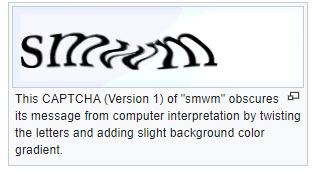
We all have used captcha even if we know what exactly it is. According to Wikipedia captcha is “a computer program or system intended to distinguish human from machine input, typically as a way of thwarting spam and automated extraction of data from websites.” It is used so that no one can write a script or use a bot to attack your websites. Google lately has used this tool very vigorously. It pops up in every google app you try to log into. It has several different adaptations now. It can be a scrambled text like the picture below, or an audio file or a set of multiple images.
The attack explained
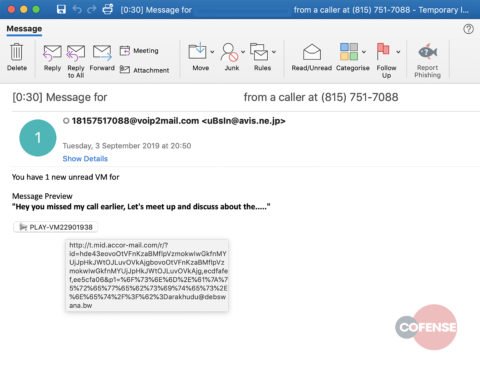
Attackers have used emails to fool the victims and victims have fallen prey to this yet again. The email said, “hey you missed my call earlier, Let’s a meetup and discuss this” attached with a link of audio with it. As soon as the user clicks this link they are redirected to a website. This website straight away asks for captcha. To be fair, the captcha is real and has no issues whatsoever. But once the user passes this captcha test, they are redirected to another page which asks the user to enter credentials of their Microsoft account. This is something that should raise suspicion because in no other app a captcha test is asked before entering your credentials. It only after entering the right username and password combination that a captcha popup appears. The captcha is used as it generates a feeling of trust among the users and they let their guard down. But it also has some other benefits.
The Dual benefits
As explained above, one purpose of using this tool was to incite trust. But according to the masterminds carrying out this attack, they had even a bigger reason for using it. Captcha tool helped them to bypass the google crawler bots and email security gateway (SEG). Google crawlers keep looking for pages of the website to check if the website is using any malicious code or any other unfair means to fool customers. But google never thought that their crawlers will be interrupted by their captcha tool. The crawlers (which are also a bot) were not able to clear the captcha tests and were never able to reach the infected landing page. Similarly for SEG, they never actually saw the malicious pages.
 The perpetrators were sophisticated in carrying out the attack. They made sure to host the captcha page and the landing page on Microsoft MSFT infrastructure. Using high-level domains, they appeared to be safe and genuine websites. According to the published reports, attackers managed to bypass this security measure for a whopping 128000 times!
The perpetrators were sophisticated in carrying out the attack. They made sure to host the captcha page and the landing page on Microsoft MSFT infrastructure. Using high-level domains, they appeared to be safe and genuine websites. According to the published reports, attackers managed to bypass this security measure for a whopping 128000 times!
Some other attacks
Several other attacks have also been carried out using captcha. In one instance, the attackers used fake captcha to fool the victims. Emails sent regarding the transaction in their bank account along with a link. The link redirects the user on a fake captcha page. This page gathers all the information about the type of device the user is using currently. As soon as it identifies the device, it automatically downloads a file on the user’s system. If the user is logged in from a phone, an apk file will be downloaded. Or if the user is logged in on a windows machine, a .exe file will be downloaded. If for some reason the system information cant be acquired, a zip will be downloaded carrying the payload.
How to prevent yourself
All these attacks are a form of email phishing only. Users should stay extremely aware while opening links from emails. Especially when an email comes from an unknown source. Second, the captcha is a tool to improve your safety but it should not be seen as a litmus test for absolute authenticity.

