On Wednesday, the tech giant Twitter witnessed the greatest cyber attack in the history of social media. To add to the extremity of the attack, “verified accounts” were compromised which included the biggest political and entertainment handles of the United States with millions of followers. These included accounts of former US President Barack Obama, tech chiefs Bill Gates, Jeff Bezos and Elon Musk and celebrities like Kim Kardashian West and institutional handles like Apple.
Twitter is the largest social media platform playing a significant role in exchanging political ideas. Renowned public figures interact with the world through short posts called “tweets”. It is undoubtedly the largest social networking service with leaders around the world posting on a daily basis.
The attack is sought to be an unprecedented attack according to the experts at Twitter. It included posting tweets from the hijacked accounts to execute a cryptocurrency scam.
The accounts fell victim to the scam via the company’s internal tools which were exploited by gathering employee privileges.
The Twitter Attack
The attack started at around 3 pm ETD, firstly compromising handles related to cryptocurrency which included @bitcoin, @ripple, @coindesk, @coinbase and @binance. Thereafter, tweets were deployed from these accounts urging followers of the cryptocurrency handles to visit the website CryptoForHealth. Within hours the website was taken down.
The next wave of the attack targetted high-profile Twitter accounts with a similar drill of tweets promoting the notorious scam. Apple and Uber were the first ones to get victimised, followed by that of Bill Gates, Elon Musk, Israel’s PM Benjamin Netanyahu and Barack Obama. Along with the handles of boxer Floyd Mayweather and celebrity Kim Kardashian. The tweets said that they would be doubling all payments done to their BTC address.

The famous Twitter handles compromised included Elon Musk, Bill Gates, Jeff Bezos, Barack Obama, Joe Biden- nominee for president Of US, Warren Buffet, Mike Bloomberg, Kanye West, Wiz Khalifa, Floyd Mayweather, Kim Kardashian, Apple and Uber.
Twitter’s Emergency Measures
Soon after the attack came under Twitter’s lens, verified accounts around the world were locked for investigation and preventing further victimizing followers and other handles. However, in these four odd-hours, the BITCOIN address received over $100,000 via 383 transactions.
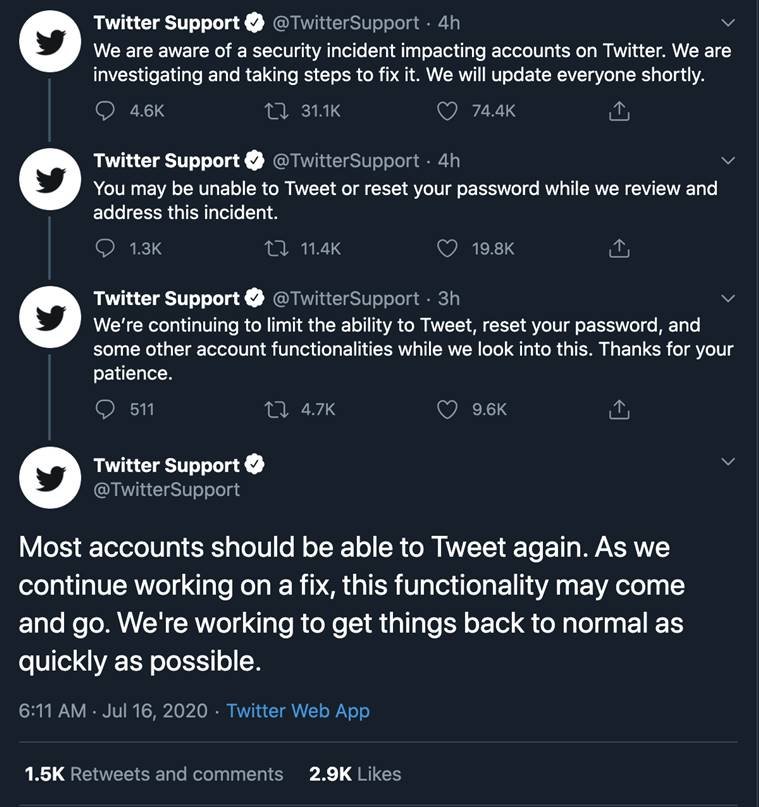
Twitter immediately halted some of the services including ‘passwords reset’, taking down every tweet containing BITCOIN address and some accounts functions were disabled. Moreover, the cryptocurrency exchange disabled further transactions to that specific BITCOIN address.
Almost all accounts were restored to normalcy, but to proceed with further investigations, Twitter informed users that some functionalities may remain unavailable.
How it happened?
The unknown threat actor schemingly executed the attack, choosing accounts with a huge follower base. Moreover, the tweets sent from genuine handles made followers believe the deal without raising any alarm.
The real reason is yet to be to known, nevertheless along with Twitter and other security firms many speculations are being made.
According to Twitter Support…
…it is a “coordinated social engineering attack” which targeted employees who have access to the company’s internal tools. But Twitter also stated that the actual cause will be told after complete investigation.
Other Theories
James McQuiggan, a security expert, stated that hackers might have convinced a Twitter employee and paid him to provide back-end access. This helped hackers to hijack accounts at a scale so vast. Hackers also harnessed other internal tools to exploit.
Other speculation came from Kelvin Coleman, executive director at National Cybersecurity Alliance, who stated that cyber crooks gained access from the inside of the company. This can possibly happen when an employee fell prey to a spear-phishing email, letting hackers steal credentials.
Undoubtedly, this attack raises concerns for other tech giants to analyse their security and policies significantly.
What if your account is hacked?
First of all, never fall prey to payments asked to made through social media as it happened in this case.
-
Hackers breach accounts usually by resetting passwords, and when that happens you are sent a verification email. So always pay attention to the emails or OTPs you get regarding password reset. Though in Twitter attack the breach was carried out via internal tools letting no such alerts!
-
Never click or open any unknown email attachment, as spear-phishing is rampant to compromise systems.
-
If you get to know about the breach, immediately inform a cyber expert and try disabling your account.
-
Keep your accounts linked with cryptocurrency wallets unlinked with any websites or with other social media platforms. This reduces the possibility of theft from crypto-wallets.
Cybercrooks are advancing and tampering with the services most of us avail, posing a great threat to our security and privacy. So beware of cybercriminals, stay updated and follow cyber ethics.


