The experts and researchers in the domain of cybersecurity have seen an upsurge in ransomware attacks. And every time it’s more lethal than the previous one. Recently, an infamous decade-old Phorpiex botnet shifts its gears from ransomware to sextortion through the infected computers present on its zombie network. Alongside sextortion, it employs crypto-clipping and crypto-jacking.
The Phorpiex botnet is ranked 2nd in the Global Threat Index in June 2020. After its rampant ransomware, Avaddon, a new Ransomware-as-a-service (RaaS) emerged last month making it to jump 13 places from 15th in May to 2nd in June. Avaddon Ransomware spread through malspam campaigns enabling threat actors to make a good fortune. The botnet has infected 2% of the organisations in the world.
About
Also known as Trikbot, Phorpiex botnet emerged about a decade ago primarily attacking systems with its various ransomware viruses through spear-phishing emails. With over 500,000 computers infected the popular malware involves GrandCrab, Pony and Pushdo to monetise Phorpiex through crypto-mining and sextortion scams. The latter is the major source of revenue for Trikbot.
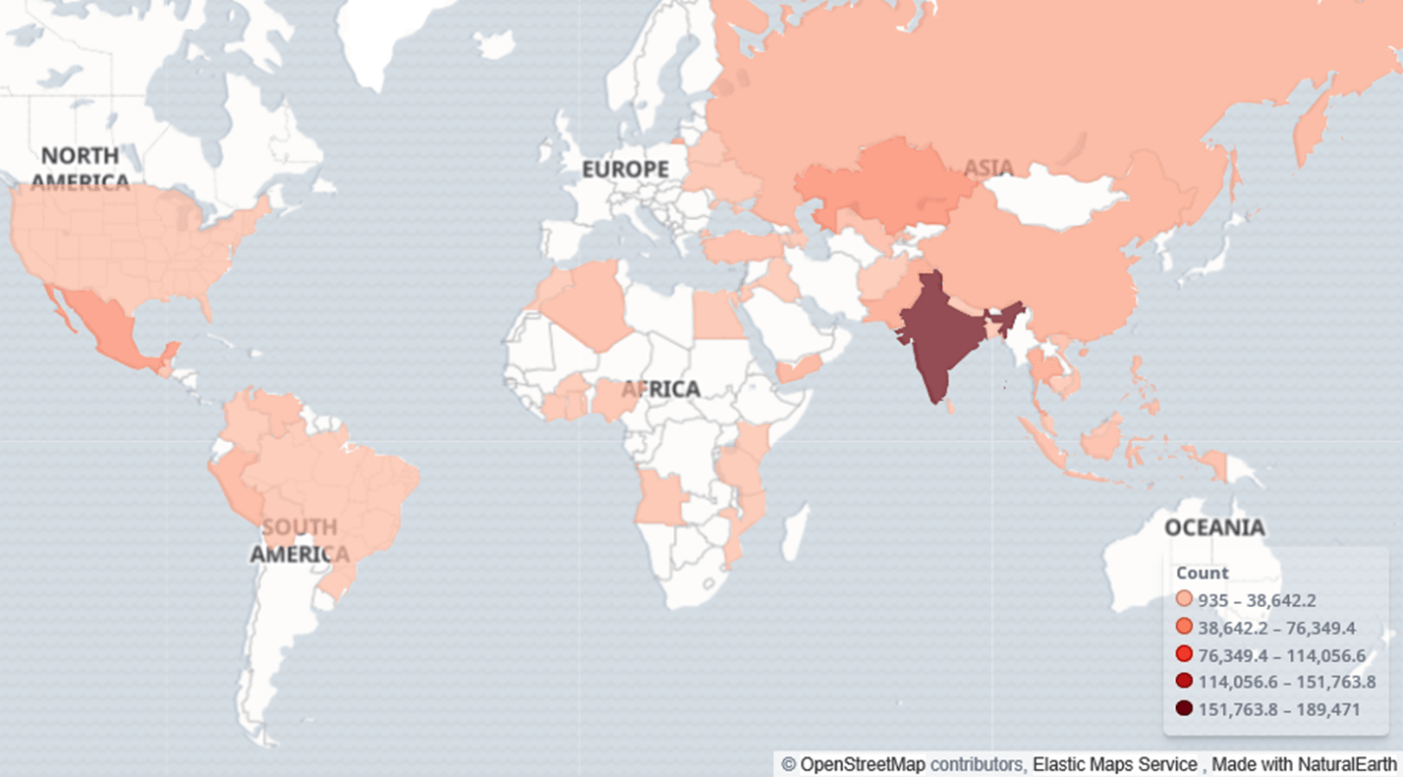
The botnet hosts are primarily located in Asia. The most significant parts of the botnet are located in India, China, Thailand, and Pakistan. There are also bots present in the US, Mexico, and many African countries. Europe is almost unaffected by the botnet.
The main ways the botnet is monetized:
-
Crypto-clipping: The only way to transfer crypto-currency without additional devices is to copy the address to the clipboard and then insert it in a corresponding field in a wallet application. The malware alters crypto wallet addresses in a clipboard, and the money is transferred to the wallet that belongs to the malware operators.
-
Crypto-jacking: It is the unauthorized use of someone else’s computer to mine cryptocurrency. One of the final payloads loaded to Phorpiex bot-controlled computers is XMRig mining software.
-
Providing services for loading other malware (Raccoon stealer, Predator The Thief), distributing ransomware
However, Phorpiex Botnet is spotted in procuring cash through a five-month campaign on a new form of revenue generation: Widescale Sextortion.
Sextortion is a type of attack where bad actors email spam messages to victims claiming to have sexual content and private data on the recipient — then, they demand a blackmail payment in exchange for not exposing the supposedly hacked data. Most of the time, the attackers are merely bluffing and hoping the intended victims will fall for the scare tactics.
After the termination of Grandcrab, Phorpiex botnet has continued infecting machines by sending emails from the infected systems.
Methodology
The botnet launches millions of emails with a malicious payload to compromise the host systems. The zombie network uses Avaddon ransomware in the in this campaign.
As mentioned earlier, this ransomware emerged at the beginning of June and Phorpiex attempts to lure victims in opening an infected email attachment. The phishing email consists of a wink emoji as the subject along with a ZIP file attachment.
The botnet downloads millions of email addresses with their corresponding credentials from the Dark Net using the command-and-control (C2) servers. Researchers noticed at least 20,000 emails in a single database and they observed between 325 and 1,363 email databases on the C2 server.
Moreover, the blackmailing email starts with a string containing the password of the victim with exacerbates the threat by showing that the actor knows the password.
Sextortion Email
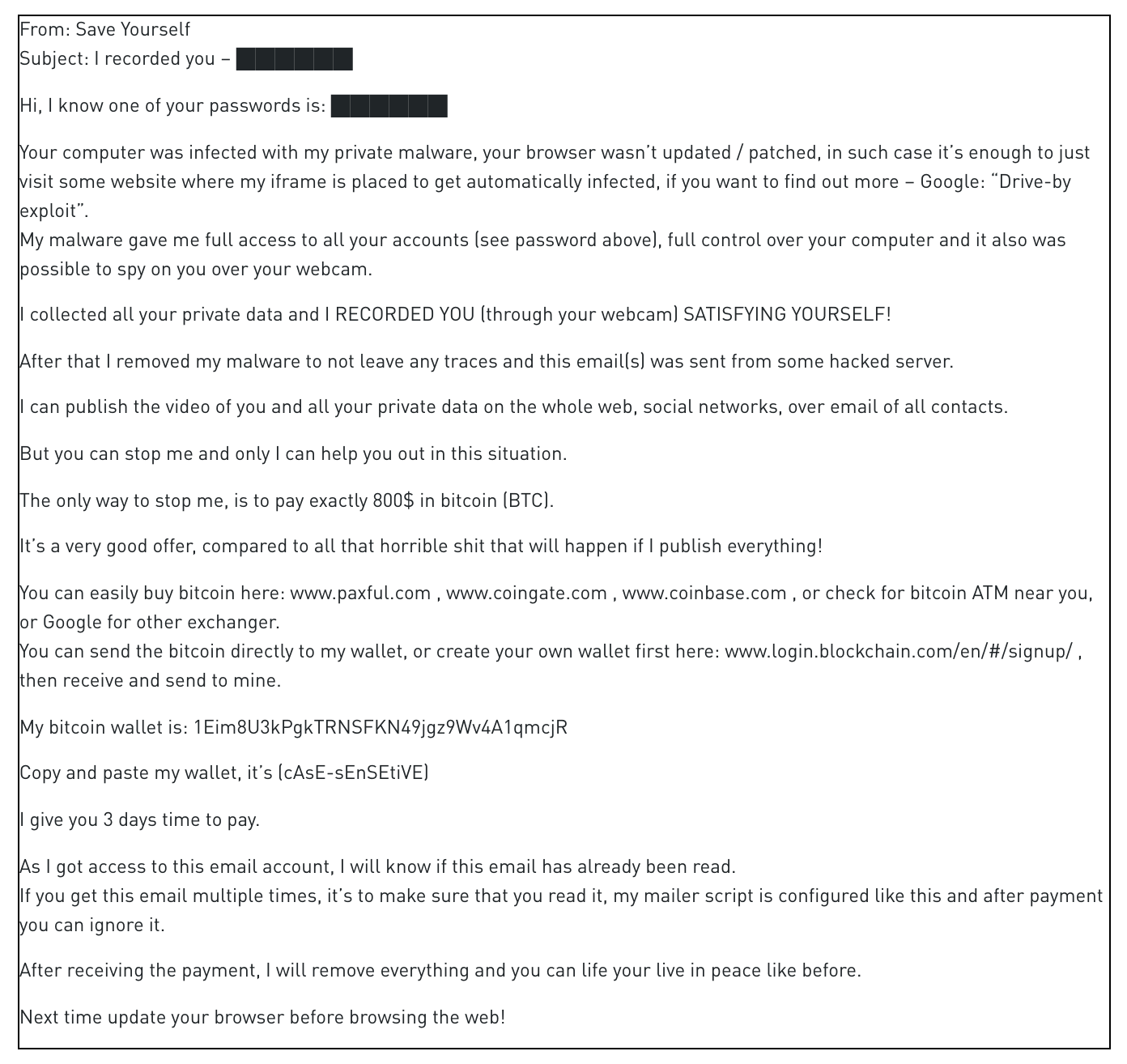
A typical sextortion email starts with the victim’s password. The email then states that the victim’s machine is infected with the malware which has gathered all private explicit content. Furthermore, the email threatens to publish the content online and send it to the emails in the victim’s contact list unless they are paid $800 in Bitcoin.
According to the researchers, Phorpiex botnet can produce 30,000 malspams per hour.
In the five-month campaign, the threat actors procured more than 14 Bitcoin.
Stay Safe from Phorpiex Botnet
-
According to Check Point, “Organisations should educate employees about how to identify the types of malspam that carry these threats, such as the latest campaign targeting users with emails containing a wink emoji, and ensuring they deploy security that actively prevents them from infecting their networks”.
-
Never click on attachments from unknown emails. In the majority of the cases, malicious campaigns penetrate a system through spear-phishing emails. Likewise in Phorpiex botnet attacks.
-
Avoid clicking links in emails. Hover the cursor over the link to verify that the URL matches with the anchor’s text and email’s stated destination.
-
If you encounter with such an email, don’t panic. Inform the IT Dept. and the police without hesitation.
Stay Safe, Stay Updated.


