WHO IS THE LAZARUS GROUP?
Lazarus Group also known as the Guardians of Peace is a gathering of cybercriminals consisting of an obscure number of individuals. The term “Lazarus” has been derived from Hebrew word “Eleazar” which meant ‘GOD HAS HELPED‘.While very little is known about the Lazarus Group, technical analysts have ascribed numerous cyber attacks to their name in the course of the last 10 years. Initially, the Lazarus Group was just like any other criminal group. However, the group has now been assigned as an Advanced tenacious danger due to its expected nature, threat, and wide exhibit of techniques utilized while carrying out an operation. Names given by Cybersecurity firms incorporate HIDDEN COBRA (by the United States Intelligence Community) and Zinc (by Microsoft).

ATTACKS LED BY THE LAZARUS GROUP
The first and the most-well known attack that the group is responsible for is known as “Operation Troy“, which occurred from 2009–2012. This was a digital-espionage crusade that used unsophisticated Distributed Denial- of- Service attack(DDoS) methods to focus on the South Korean government in Seoul. They are additionally responsible for attacks in 2011 and 2013. It is conceivable that they were likewise behind a 2007 attack focusing on South Korea; however that is as yet uncertain. An outstanding attack that the group is known for is the 2014 attack on Sony Pictures. The Sony attack utilized progressively modern systems and featured how cutting-edge and advanced the group has turned out within a very short span of time.
The Lazarus Group were accounted for have taken $12 million from the Banco del Austro in Ecuador and US$1 million from Vietnam’s Tien Phong Bank in 2015.They have also additionally targeted banks in Poland and Mexico. The 2016 bank heist involved an attack on the Bangladesh Bank, effectively taking US$81 million and was believed to be carried out by the Lazarus Group. In 2017, the Lazarus group was accounted for have taken US$60 million from the Far Eastern International Bank of Taiwan despite the fact that the real sum taken was hazy and the greater part of the assets were recovered.
It isn’t exactly clear who is the main force behind the group, yet media reports have stated that the group has connections to North Korea. Kaspersky Lab revealed in 2017 that the Lazarus Group in general would focus on spying and penetration cyber attacks while a sub-bunch inside their association, which Kaspersky called Bluenoroff, had some expertise in money related cyber attacks. Kaspersky found a link (IP address) between different attacks worldwide with Bluenoroff and North Korea thus indicating their connection.
Notwithstanding, Kaspersky additionally recognized that the redundancy of the code could be a “false banner” intended to deceive examiners and stick the attack on North Korea, given that the overall WannaCry worm digital attack duplicated methods from the NSA too. This ransom ware used a NSA exploit known as EternalBlue that a hacker group known as Shadow Brokers made it public in April 2017. Symantec announced in 2017 that it was “almost certain” that Lazarus was behind the WannaCry attack.
LATEST CRYPTOCURRENCY ATTACK
The notorious Lazarus Group, assumed to be from North Korean are back in real life. Technical analysts have found the hackers focusing their targets on Windows and Mac clients with another methodology. In particular, the Lazarus Group has built up fake cryptographic money programming software to snoop into the gadgets of targeted victims. Researchers from the Malware Hunter Team have found another attack from the North Korean programmers whose main objective is to target the Windows and Mac gadgets. The Lazarus Group is presently intending to supply casualties with fake cryptocurrency programming software. This device enables the hackers to remotely assume total control over the victim’s gadgets. The specialists have shared a detailed thread on Twitter about this malware in order to make people more aware and alert about similar kinds of cyber attacks. As explained, the hackers have even made an authentic looking website of a fake organization. Named as JMT Trading, the firm professes to create software for digital money exchanging.

HOW WAS THE ATTACK CARRIED OUT?
The website enabled guests to download the software from GitHub, where the hackers had already put the product code and set apart an open source. A similar website had separate executables for Windows and Mac too. While the open-source code apparently was aimed at Linux clients. The system looks very straightforward and genuine .The open-source code additionally gave no indications of perniciousness. Be that as it may, when a client downloaded the product, the installer likewise introduced an auxiliary executable record “CrashReporter.exe” on the framework. This part, present in the %AppData%\JMTTrader folder was the actual malware filling in as an indirect access. This program, by means of a scheduled undertaking, executed each time a client signed in, and, with each execution, the program reached the C&C to get and execute directions. Initial investigation of the malware demonstrated it effectiveness against Mac gadgets. Moreover on further examination, it ended up being similarly as powerful against Windows frameworks also.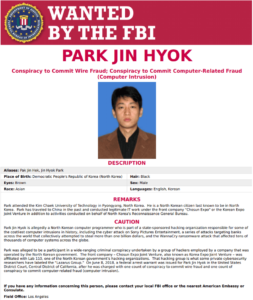
The Group that is suspected of being behind this Cryptocurrency Malware Attack enabled the researchers through preliminary investigation to set up a connection between this malware conspire and the North Korean hacking bunch Lazarus. They could set up this connection considering various similarities between this attack and the recently found attack on macOS that surfaced online back in August 2018. From the malware investigation there is a nonattendance of an Apple designer ID signature and the impersonation of digital money firms. Thus, establishing a solid connection between the two attacks. Though, the malware sample was unique and different from each other. Following the reports with respect to the malware, the hackers immediately removed the website. For the time being, the JMT Trading GitHub archive is inaccessible. Furthermore, the JMT Trading site is likewise down.
SHOULD YOU BE WORRIED?
Indeed, however not to the degree you may think. Lazarus Group exercises focus on monetary profit, just as accomplishing the political objectives of the North Korean system. Given that North Korea’s expressed political targets tend to hyper center around local clashes with South Korea and Japan, organizations outside of that circle most likely are at a generally safe position from these politically-propelled cyberattacks



